Protecting vital information assets requires a comprehensive strategy involving the duplication and relocation of data to a separate physical location. This process ensures business continuity by safeguarding against data loss from various threats, including hardware failures, cyberattacks, natural disasters, and human error. For instance, a company might replicate its server data to a geographically distant facility or utilize cloud-based services for data preservation.
Maintaining replicated information in a geographically separate environment is crucial for organizational resilience. It minimizes downtime following unforeseen events, enabling swift recovery and mitigating financial losses. Historically, organizations relied on physical tapes and offsite vaults. However, advancements in technology have led to more efficient and secure methods, such as cloud-based solutions offering scalability and automated processes. This evolution reflects the growing importance of data protection in an increasingly interconnected and data-reliant world.
Understanding the intricacies of protecting information assets is paramount in today’s business landscape. The following sections delve into key aspects of this multifaceted process, covering best practices, technological advancements, and strategic considerations for implementing a robust and effective solution.
Essential Practices for Data Protection and Recovery
Protecting valuable data and ensuring business continuity requires a proactive approach. The following practices offer guidance for establishing a robust data protection and recovery strategy.
Tip 1: Implement the 3-2-1 Rule. Maintain at least three copies of data, on two different media types, with one copy stored offsite.
Tip 2: Regularly Test Restorations. Periodic testing validates the recoverability of data and identifies potential issues before a real disaster strikes.
Tip 3: Encrypt Data at Rest and in Transit. Encryption safeguards sensitive information from unauthorized access, both during storage and transmission.
Tip 4: Employ Versioning and Retention Policies. Retain multiple versions of data to recover from accidental deletions or ransomware attacks. Define clear retention policies based on regulatory requirements and business needs.
Tip 5: Choose the Right Storage Medium. Consider factors such as cost, scalability, accessibility, and security when selecting storage solutions (e.g., cloud, tape, hard drives).
Tip 6: Document the Recovery Process. A well-documented recovery plan ensures a swift and organized response during a disaster, minimizing downtime and data loss.
Tip 7: Consider Geographic Diversity. Storing data in geographically dispersed locations protects against regional disasters and ensures business continuity.
Tip 8: Regularly Review and Update the Strategy. The data protection strategy should be reviewed and updated periodically to adapt to changing business needs, evolving threats, and technological advancements.
Implementing these practices creates a strong foundation for data resilience, enabling organizations to withstand disruptions and maintain business operations.
By incorporating these strategies, organizations can effectively safeguard their data and ensure uninterrupted operations, even in the face of unforeseen events.
1. Geographic Redundancy
Geographic redundancy forms a cornerstone of robust offsite data backup and disaster recovery strategies. It mitigates the risk of data loss due to localized events by distributing data across geographically dispersed locations. This distribution ensures business continuity even if one location becomes inaccessible.
- Data Replication Across Multiple Sites
Data is replicated and maintained in multiple geographically separated data centers. This approach ensures data availability even if one data center experiences an outage due to natural disasters, power failures, or other unforeseen events. For example, a company might store data in data centers located on both the East and West Coasts of the United States.
- Minimizing Regional Disaster Impact
Storing data in geographically diverse locations safeguards against regional disasters. If a hurricane impacts one coastal region, the data remains safe and accessible in another unaffected region. This redundancy minimizes downtime and ensures business operations can continue uninterrupted.
- Latency and Performance Considerations
While geographic redundancy enhances data resilience, it also introduces latency considerations. Accessing data stored in a distant location might experience slightly higher latency compared to accessing local data. Strategies like content delivery networks (CDNs) can mitigate this issue by caching data closer to users. Balancing redundancy with performance requires careful planning and optimization.
- Compliance and Data Sovereignty
Geographic redundancy can play a crucial role in meeting regulatory requirements, particularly concerning data sovereignty. Certain regulations mandate data storage within specific geographic boundaries. Organizations must adhere to these regulations when implementing geographically redundant data storage solutions. For instance, healthcare data subject to HIPAA must be stored securely within designated jurisdictions.
By distributing data across multiple geographic locations, organizations establish a robust defense against data loss and ensure business continuity. While latency and regulatory considerations require careful planning, the benefits of geographic redundancy are essential for organizations prioritizing data resilience and operational stability. A well-designed geographically redundant strategy strengthens disaster recovery plans and enables organizations to withstand unforeseen events with minimal disruption.
2. Secure Storage Solutions
Secure storage solutions form an integral part of offsite data backup and disaster recovery. Data integrity and confidentiality rely on robust security measures implemented within the storage infrastructure. Without adequate security, backed-up data remains vulnerable to unauthorized access, breaches, and potential manipulation, negating the purpose of offsite protection. For instance, an organization utilizing cloud storage for backups must ensure the chosen provider implements strong encryption, access controls, and multi-factor authentication to prevent unauthorized data access. Compromised backups can have severe consequences, including data loss, reputational damage, regulatory penalties, and business disruption.
Several factors contribute to the security posture of storage solutions. Encryption, both at rest and in transit, safeguards data from unauthorized decryption. Access controls restrict data access to authorized personnel only, minimizing the risk of insider threats or accidental data exposure. Regular security audits and vulnerability assessments identify and address potential weaknesses in the storage infrastructure. Furthermore, adherence to industry best practices and regulatory frameworks, such as ISO 27001 and GDPR, ensures a comprehensive and compliant security approach. Employing a combination of physical and logical security measures safeguards data against diverse threats. Physical security protects the physical infrastructure hosting the storage, while logical security controls access to data through software and network configurations.
Secure storage solutions are not merely a component but a fundamental requirement for effective offsite data backup and disaster recovery. Implementing robust security measures within the storage environment ensures data confidentiality, integrity, and availability. Failure to prioritize security can undermine the entire disaster recovery strategy, leaving organizations vulnerable to data breaches and operational disruptions. A comprehensive security approach, encompassing encryption, access controls, regular audits, and adherence to best practices, is paramount for ensuring data resilience and maintaining business continuity. Choosing a reputable storage provider with a proven track record of security is equally critical. This careful selection ensures that the chosen solution aligns with organizational security requirements and regulatory obligations.
3. Automated Backup Processes
Automated backup processes are fundamental to effective offsite data backup and disaster recovery. Manual backups are prone to human error and often lack the consistency required for reliable recovery. Automation eliminates these shortcomings, ensuring regular, dependable backups and streamlining the recovery process. Without automation, maintaining up-to-date offsite backups becomes challenging, increasing the risk of data loss and extending recovery times.
- Scheduled Backups
Automated systems allow for scheduled backups, ensuring data is regularly copied to the offsite location. This eliminates the need for manual intervention, reducing the risk of missed backups and ensuring data consistency. For example, a system can be configured to perform incremental backups every hour and full backups every weekend. This consistent approach maintains a readily available recovery point, minimizing potential data loss in a disaster scenario.
- Reduced Human Intervention
Minimizing human involvement reduces the likelihood of errors and improves efficiency. Automation streamlines the backup process, freeing up IT staff for other critical tasks. Rather than manually initiating and monitoring backups, automated systems handle these tasks independently, reducing the potential for human error and improving overall operational efficiency.
- Real-Time Data Replication
Some automated solutions offer real-time data replication, ensuring near-instantaneous backups and minimizing data loss in case of a system failure. This capability is crucial for applications requiring high availability and minimal recovery point objectives (RPOs). For instance, financial institutions often employ real-time replication to maintain continuous data protection and ensure business continuity.
- Integration with Disaster Recovery Systems
Automated backups seamlessly integrate with disaster recovery systems, enabling rapid and automated recovery in case of an outage. This integration streamlines the recovery process, reducing downtime and minimizing the impact on business operations. Automated failover mechanisms, triggered by pre-defined events, can automatically restore data from the offsite backup, ensuring business continuity.
Automated backup processes form a crucial link between data protection and successful disaster recovery. By automating backups, organizations ensure data integrity, minimize recovery time, and enhance overall business resilience. This automation eliminates the risks associated with manual processes, paving the way for efficient and reliable disaster recovery. The integration of automated backups with comprehensive disaster recovery plans allows for a swift and coordinated response to unforeseen events, safeguarding critical data and maintaining business operations.
4. Rapid Recovery Mechanisms
Rapid recovery mechanisms are essential for minimizing downtime and data loss following a disruption. Offsite data backup storage provides the foundation for recovery, but the speed of restoration is equally critical. The connection between rapid recovery and offsite backup lies in the ability to quickly access and restore the backed-up data when needed. Without rapid recovery capabilities, even readily available offsite backups cannot prevent extended periods of business disruption. For instance, a manufacturing company experiencing a server failure could face significant production delays if its recovery process takes days rather than hours. Rapid recovery mechanisms, therefore, directly influence the overall effectiveness of the disaster recovery plan. Factors such as network bandwidth, data restoration speed, and automated recovery procedures play key roles in achieving rapid recovery. The recovery time objective (RTO) defines the maximum acceptable downtime, while the recovery point objective (RPO) defines the maximum acceptable data loss. These objectives guide the design and implementation of rapid recovery mechanisms.
Real-world examples underscore the importance of rapid recovery. A financial institution relying on real-time data processing requires near-instantaneous recovery capabilities to avoid significant financial losses and maintain customer trust. In contrast, a small business with less critical data might tolerate a longer recovery period. The specific requirements for rapid recovery vary based on the organization’s industry, size, and data criticality. However, the underlying principle remains consistent: minimizing downtime and data loss are crucial for business continuity. Implementing solutions like automated failover systems, redundant hardware, and high-bandwidth connections to the offsite backup location contributes to rapid recovery. Testing these mechanisms regularly ensures their effectiveness and readiness in a real disaster scenario. Failure to prioritize rapid recovery can lead to extended outages, reputational damage, and financial repercussions.
Rapid recovery is not merely a desirable feature but a critical component of a comprehensive disaster recovery strategy. Offsite backups provide the data safety net, but rapid recovery mechanisms determine how quickly an organization can resume operations after a disruption. The interdependence between these two aspects necessitates careful planning and implementation. Organizations must define their RTO and RPO, invest in appropriate technologies, and rigorously test their recovery processes to ensure business resilience. Ignoring the importance of rapid recovery can jeopardize the effectiveness of the entire disaster recovery plan, leaving organizations vulnerable to extended downtime and potentially irreversible damage.
5. Regulatory Compliance
Regulatory compliance plays a crucial role in offsite data backup storage and disaster recovery. Various regulations, such as GDPR, HIPAA, and PCI DSS, mandate specific data protection and recovery requirements. These regulations often dictate data retention policies, encryption standards, and geographic restrictions for data storage. Non-compliance can lead to significant fines, legal repercussions, and reputational damage. Organizations must ensure their offsite backup and disaster recovery strategies align with these regulations to avoid penalties and maintain a strong security posture. For example, GDPR mandates strict data protection requirements for European Union citizens’ data, including offsite backup and disaster recovery provisions. Healthcare organizations handling patient data must adhere to HIPAA regulations, which dictate specific security and privacy standards for protected health information (PHI). Similarly, businesses processing credit card transactions must comply with PCI DSS, requiring secure storage and processing of cardholder data.
Failing to comply with relevant regulations can have far-reaching consequences. Financial penalties can be substantial, impacting an organization’s bottom line. Legal action can result in protracted lawsuits and further financial strain. Reputational damage can erode customer trust, impacting brand image and future business prospects. Therefore, regulatory compliance is not merely a legal obligation but a critical aspect of responsible data management and disaster recovery planning. For example, a data breach resulting from inadequate offsite backup security can lead to regulatory investigations and penalties if the organization fails to meet the required data protection standards. Conversely, demonstrating compliance with relevant regulations can strengthen an organization’s reputation, build customer trust, and enhance its competitive advantage.
Integrating regulatory compliance into offsite data backup and disaster recovery strategies requires a proactive approach. Organizations must identify the specific regulations applicable to their industry and data types. Implementing appropriate security measures, such as encryption, access controls, and regular audits, is essential for demonstrating compliance. Choosing compliant storage solutions and providers is crucial, ensuring data is stored and managed according to regulatory mandates. Regularly reviewing and updating the offsite backup and disaster recovery plan ensures ongoing compliance with evolving regulatory requirements. Integrating compliance considerations from the outset streamlines the process and minimizes the risk of non-compliance. Ultimately, adhering to regulatory requirements strengthens data protection, minimizes the risk of legal repercussions, and enhances an organization’s reputation for responsible data management.
6. Comprehensive Testing
Comprehensive testing forms an indispensable component of robust offsite data backup and disaster recovery strategies. It validates the effectiveness of the implemented solution, verifying the ability to restore data and resume operations within acceptable timeframes. Without thorough testing, organizations cannot confidently rely on their disaster recovery plans, risking extended downtime, data loss, and reputational damage. Testing unveils potential weaknesses in the system, allowing for proactive remediation before a real disaster strikes. A well-defined testing strategy encompasses various scenarios, including hardware failures, cyberattacks, natural disasters, and human error. This approach ensures preparedness for diverse disruptions, minimizing the impact of unforeseen events. For example, simulating a ransomware attack can reveal vulnerabilities in the backup process, allowing for improvements in security and recovery procedures. Regularly scheduled tests, encompassing different disaster scenarios, ensure the ongoing effectiveness of the disaster recovery plan, adapting to evolving threats and system changes.
Practical examples highlight the significance of comprehensive testing. A hospital relying on electronic health records must rigorously test its disaster recovery plan to ensure continuous access to patient data during an outage. Testing might involve simulating a power failure and verifying the ability to restore critical systems from the offsite backup within the required timeframe. In the financial sector, regular testing ensures compliance with regulatory requirements and minimizes the risk of financial losses during a system disruption. Testing scenarios might include simulating a cyberattack and verifying the ability to restore trading systems and customer data quickly and securely. These examples underscore the importance of tailoring the testing strategy to the specific needs and risks of each organization.
Comprehensive testing provides crucial assurance and practical insights into the effectiveness of offsite data backup and disaster recovery plans. It bridges the gap between theory and practice, identifying potential weaknesses and enabling proactive remediation. Regularly testing various disaster scenarios, combined with continuous improvement based on test results, ensures organizations can confidently withstand disruptions, minimize downtime, and protect their valuable data assets. Failing to prioritize comprehensive testing can undermine the entire disaster recovery strategy, leaving organizations vulnerable to unforeseen events and their potentially devastating consequences. A proactive and rigorous testing approach, integrated into the overall disaster recovery framework, is paramount for ensuring business resilience and maintaining operational stability.
7. Cost-Effective Strategies
Cost-effective strategies are essential for implementing sustainable offsite data backup and disaster recovery solutions. Balancing robust data protection with budgetary constraints requires careful planning and resource allocation. Organizations must consider the total cost of ownership (TCO), including hardware, software, bandwidth, maintenance, and potential downtime costs. Choosing the right combination of technologies and services, while optimizing resource utilization, ensures cost-efficiency without compromising data resilience. For example, leveraging cloud-based backup solutions can offer scalability and cost savings compared to maintaining physical offsite infrastructure. However, organizations must carefully evaluate cloud storage pricing models and data transfer costs to avoid unexpected expenses. Another cost-effective approach involves tiered storage, utilizing different storage media based on data criticality and access frequency. Less critical data can be stored on lower-cost media, while frequently accessed data resides on higher-performance storage. Implementing data deduplication and compression techniques further optimizes storage utilization and reduces costs.
Real-world scenarios demonstrate the practical significance of cost-effective strategies. A small business with limited resources might opt for a hybrid approach, combining local backups with cloud-based storage for critical data. This strategy balances cost-efficiency with adequate data protection. Larger enterprises, on the other hand, might invest in dedicated offsite infrastructure with advanced features, justifying the higher cost with the need for enhanced security and rapid recovery capabilities. Another example involves leveraging virtualization technologies to consolidate backup infrastructure, reducing hardware and maintenance costs. Choosing open-source backup software can also offer significant cost savings compared to proprietary solutions. The selection of specific strategies depends on the organization’s size, industry, data criticality, and budget constraints. However, the underlying principle remains consistent: maximizing data protection while minimizing costs.
Cost-effective strategies are not merely about minimizing expenses but about optimizing resource allocation to achieve the desired level of data protection. Balancing cost-efficiency with security, performance, and regulatory compliance requires careful consideration of various factors. Organizations must assess their specific needs, evaluate available technologies, and develop a tailored strategy that aligns with their budget and business objectives. Failure to prioritize cost-effectiveness can lead to unsustainable solutions, potentially jeopardizing data protection in the long run. A proactive and well-defined cost-effective strategy ensures organizations can implement robust offsite data backup and disaster recovery solutions without exceeding budgetary constraints, safeguarding valuable data assets while maintaining financial stability.
Frequently Asked Questions
This section addresses common inquiries regarding offsite data backup storage and disaster recovery, providing clarity on key aspects of these crucial processes.
Question 1: How frequently should offsite backups be performed?
Backup frequency depends on data criticality, recovery point objectives (RPOs), and business requirements. Critical data requiring minimal data loss might necessitate real-time or near real-time replication. Less critical data might tolerate less frequent backups, such as daily or weekly.
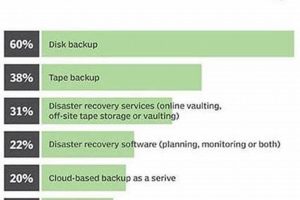
Question 2: What are the different types of offsite backup storage solutions available?
Options include cloud-based services, dedicated offsite servers, and physical media storage (e.g., tapes). Cloud-based solutions offer scalability and accessibility, while dedicated servers provide greater control. Physical media remains a viable option for archival purposes.
Question 3: What is the difference between disaster recovery and business continuity?
Disaster recovery focuses on restoring IT infrastructure and data after a disruption. Business continuity encompasses a broader scope, addressing overall business operations and ensuring minimal disruption to critical functions, including IT systems.
Question 4: How is data security ensured during offsite storage and transfer?
Encryption, both at rest and in transit, protects data confidentiality. Access controls restrict data access to authorized personnel. Secure storage facilities with physical and logical security measures further enhance data protection.
Question 5: What are the key considerations when choosing an offsite backup provider?
Factors include security certifications (e.g., ISO 27001, SOC 2), data storage location, service level agreements (SLAs) guaranteeing recovery times, and overall cost-effectiveness.
Question 6: How often should disaster recovery plans be tested?
Regular testing, at least annually, validates the plan’s effectiveness. More frequent testing might be necessary for critical systems or following significant changes to the IT infrastructure. Testing should encompass various disaster scenarios to ensure comprehensive preparedness.
Understanding these key aspects of offsite data backup storage and disaster recovery enables informed decision-making and strengthens data resilience.
The subsequent sections will explore specific technologies and best practices for implementing effective offsite backup and disaster recovery solutions.
Conclusion
Offsite data backup storage and disaster recovery form a critical cornerstone of modern data management. This exploration has highlighted the multifaceted nature of these processes, encompassing secure storage solutions, automated backup procedures, rapid recovery mechanisms, regulatory compliance, comprehensive testing, and cost-effective strategies. Each element plays a vital role in ensuring data resilience and business continuity in the face of unforeseen disruptions. The evolving threat landscape, coupled with increasing reliance on data, necessitates a proactive and comprehensive approach to data protection. Ignoring these critical aspects can lead to significant financial losses, reputational damage, and operational paralysis.
Safeguarding valuable data assets requires a continuous commitment to best practices and evolving technologies. Organizations must prioritize data protection as an integral part of their overall risk management strategy. Investing in robust offsite data backup storage and disaster recovery solutions is not merely a prudent measure but a strategic imperative for navigating the complexities of the modern digital landscape and ensuring long-term success. The ability to withstand disruptions and recover swiftly from unforeseen events will increasingly differentiate resilient organizations in an interconnected and data-driven world.