
The space shuttle Challenger disintegrated 73 seconds into its flight on January 28, 1986. The subsequent search and recovery operation in the Atlantic Ocean, a complex undertaking involving NASA, the U.S. Navy,... Read more »
A strategy designed to restore data and systems following a ransomware attack is critical for business continuity. This involves a structured approach that outlines procedures for identifying the attack, isolating affected systems,... Read more »

A template for restoring information technology infrastructure and operations after an unforeseen disruptive event provides a structured approach to minimizing downtime and data loss. Such a template typically includes documented procedures for... Read more »
A documented process enabling organizations to resume mission-critical functions following disruptive events like natural disasters, cyberattacks, or equipment failures involves restoring data, applications, and infrastructure to operational status. A practical illustration involves... Read more »
Swift identification of disruptive events, whether natural disasters, cyberattacks, or hardware failures, is paramount for effective disaster recovery. This allows organizations to initiate recovery processes promptly, minimizing downtime and potential data loss.... Read more »

Disaster recovery strategies encompass a range of approaches designed to restore IT infrastructure and operations following disruptive events. These strategies vary in their complexity, cost, and recovery time objectives (RTOs). For example,... Read more »
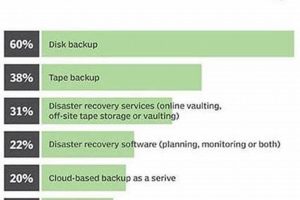
Applications, systems, and procedures that allow an organization to restore its IT infrastructure and data after a disruptive event, such as a natural disaster, cyberattack, or equipment failure, comprise a critical component... Read more »
A template document in Portable Document Format (PDF) provides a pre-designed framework for organizations to create a strategy for restoring critical operations and data after an unforeseen disruptive event. This framework typically... Read more »

Organizations rely on information technology systems for critical operations. An unexpected outage, caused by natural disasters, cyberattacks, or even simple human error, can disrupt business processes, resulting in significant financial losses and... Read more »

Organizations depend on their information systems and operational processes. A framework designed to safeguard these critical functions against disruptions involves two key components. The first focuses on restoring IT infrastructure and systems... Read more »


